Secure Information Continuum for 965935900, 923061800, 3032095563, 3487934711, 120065363, 6514148203
The Secure Information Continuum for identifiers such as 965935900 and 923061800 outlines a systematic approach to data protection. It emphasizes the need for comprehensive risk assessments at every stage of the data lifecycle. This methodical integration of security measures not only ensures regulatory compliance but also safeguards organizational integrity. As organizations strive to enhance their security frameworks, understanding the implications of this continuum becomes crucial for effective risk management. What strategies can be employed to optimize these phases?
Understanding the Secure Information Continuum
Although the concept of the Secure Information Continuum may initially appear complex, it fundamentally represents the seamless integration of security measures throughout the lifecycle of data.
This approach necessitates meticulous risk assessment at each stage, ensuring that vulnerabilities are identified and mitigated.
Key Phases of Data Protection
A comprehensive understanding of the key phases of data protection is essential for organizations aiming to safeguard sensitive information effectively.
These phases encompass the entire data lifecycle, from creation and storage to sharing and deletion.
Effective risk management strategies must be integrated throughout to identify vulnerabilities, ensuring a proactive approach to data security and compliance with regulations, ultimately protecting organizational integrity and privacy.
Implementing Best Practices for Data Security
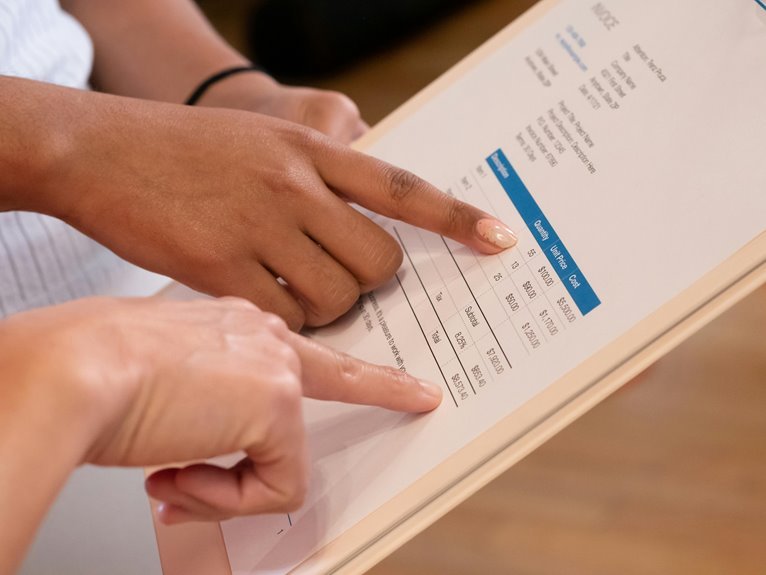
Implementing best practices for data security requires a structured approach that encompasses various strategies and technologies. Key components include data encryption to safeguard sensitive information, access controls to limit unauthorized usage, and robust threat detection systems.
Additionally, effective incident response plans, regular risk assessments, and ongoing security training for personnel are essential to mitigate vulnerabilities and empower individuals in maintaining a secure information environment.
Building Trust Through Compliance and Transparency
While organizations strive to enhance their data security measures, building trust with stakeholders hinges significantly on compliance and transparency.
Effective trust frameworks and robust compliance strategies are essential in fostering this relationship. By adhering to regulatory standards and openly communicating practices, organizations can alleviate concerns, thereby establishing a foundation of trust.
Ultimately, transparency serves as a catalyst for stakeholder confidence and enduring partnerships.
Conclusion
In conclusion, the Secure Information Continuum underscores the necessity of a comprehensive approach to data security, addressing vulnerabilities across all stages of the data lifecycle. By meticulously implementing risk assessments and best practices, organizations not only safeguard their information but also bolster compliance and foster stakeholder trust. Ultimately, adopting this proactive strategy allows organizations to stay one step ahead, ensuring that they do not just weather the storm but thrive amidst the challenges of an evolving digital landscape.